Petaling Jaya (23 January 2017) — Kaspersky Lab announced a specialized solution to secure critical infrastructure and industrial facilities in Malaysia. Kaspersky Industrial CyberSecurity delivers a unified, holistic approach to IT security for industrial facilities, combining the company’s leading technologies, services and intelligence in one unique package.
Malaysia is highly dependent on its industrial sector across manufacturing, infrastructure, power production, photovoltaics, automative construction and defence. The industrial sector contributed 36.8% or over a third of the country’s GDP in 2014 and employed 36% of the labour force in 2012.
For perspective cyber-attacks on industrial control systems are on the increase with 67% of information & operational technology managers finding the security landscape to be critical, a 43% increase over 2015 findings..
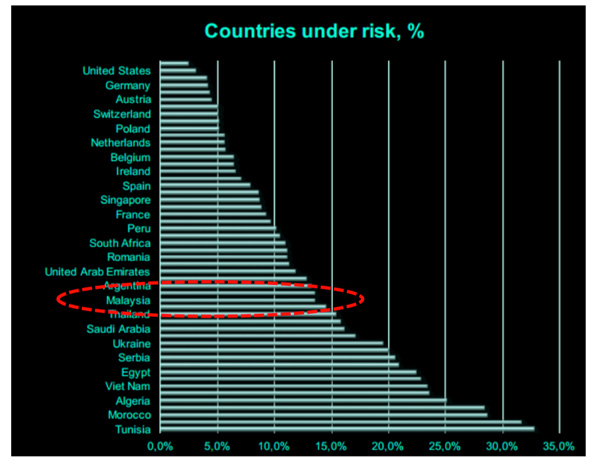
From the Kaspersky Lab Industrial Control Systems Cyber Emergency Response Team (ICS CERT) Report 2016, Malaysia has a risk score of 15% . The scoring is determined by the observability mode, security assessment and exploit prevention. . The country is also a target for cyber-attacks, ranking 66th on the Kaspersky Lab Industrial Cyberthreats Real-Time Map.
Enter Kaspersky Industrial CyberSecurity or KICS for short that radically changes the approach of traditional industrial security techniques and systems. The introduction of KICS is timely and needful as the industrial sector grows in Malaysia; and cyberthreats targetting the industry increase.
Kaspersky Industrial CyberSecurity received the World Leading Internet Scientific and Technological Achievement Award at the 3rd World Internet Conference in Wuzhen, China in 2016 for addressing the urgent need to comprehensively manage industrial cyber-risks and protect the continuity and integrity of systems that are vital to the economy, and people’s health and welfare.
“Today, the cybersecurity of industrial systems and critical infrastructures is of vital importance,” said Vikram Kalkat, Senior Key Account Manager, Kaspersky Industrial Cyber Security Global Business Development, APAC Region. “An increasing number of such systems are using devices and channels that interact with the outside world. Sometimes they use equipment that was never intended for external access, not to mention software that was created decades ago and has not been upgraded since! This is a very serious issue because not only is the continuity of the production process at stake, the environment and even human lives can be at risk. Our solution is capable of ensuring the cybersecurity of the technology cycle at all levels of the automated process control. We are also actively cooperating with manufacturers of automation systems in order to develop equipment that takes new cybersecurity standards and requirements into consideration.”
Information technologies and process automation systems are crucial to the operation of all modern industrial facilities – from power plants, refineries and assembly lines to railways, airports and smart buildings. Unlike traditional corporate IT networks, where confidentiality is the top priority, industrial control systems (ICS) demand faultless continuity and consistency of the technological process. Strict regulation and compliance can lead to unprotected operating of critical facilities if the cybersecurity measures do not meet safety requirements.
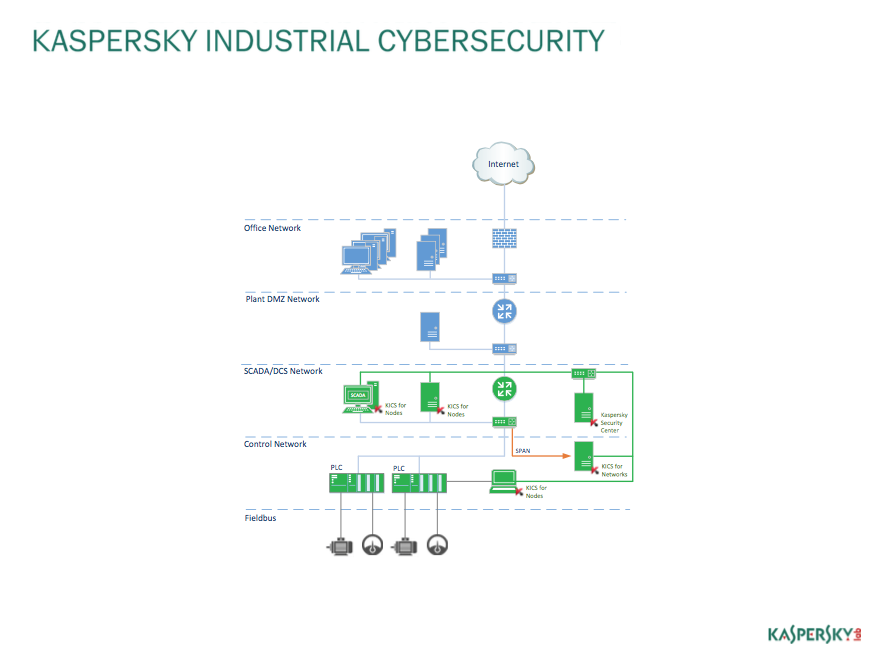
Kaspersky Industrial CyberSecurity considers all these unique requirements and delivers protection to the ICS network at the layers most vulnerable to cyber-attacks – ICS/SCADA servers, HMI panels, engineering workstations, PLCs and more – securing them from cyber-threats without affecting operational continuity and consistency of the technological process.
ICS threat detection and prevention
Traditionally, ICS organizations are not well prepared or protected to withstand cyber security attacks. The design of ICS software and hardware is hard to call secure.
To minimize the possibility of a cyber-attack, Industrial Control Systems (ICS) is supposed to be run in a physically isolated environment. However this is not always the case.Based on Industrial Control Systems Threat Landscape report, Kaspersky Lab experts revealed 17,042 ICS components on 13,698 different hosts exposed to the Internet, likely belong to large organizations. These organizations include energy, transportation, aerospace, oil and gas, chemicals, automotive and manufacturing, food and drink, governmental, financial and medical institutions. To minimize the possibility of a cyber-attack, ICS should be run in a physically isolated environment; however, the report shows that thousands of hosts are being exposed with 91.1 percent of these ICS hosts having vulnerabilities that can be exploited remotely. In addition, 3.3 percent of ICS hosts located in these organizations contain critical vulnerabilities that can be exploited remotely.
Historically, ICS operating team is not able to recognize social engineering attacks, recognize unsafe actions and become a solid stage of cyber security in their organizations. Of cause, their main task is to provide safe and reliable production process. On the other hand, the ICS organizations cannot afford significant investment into security workforce, since this is not a priority for them. The cyber security response plan may assume that some external organization is involved for incident coordination, analysis and response actions.
Kaspersky Industrial CyberSecurity offers a combination of conventional security technologies, adapted for an ICS environment, such as anti-malware protection, whitelisting and vulnerability assessment functionality. This strong foundation is further enhanced with unique technologies designed specifically for industrial environments, including integrity check for programmable logic controller (PLC), semantic monitoring of process control commands and telemetry data to detect cyber-attacks targeting the physical part of an infrastructure.
Kaspersky Industrial CyberSecurity also provides a special observability mode that focuses solely on the detection of cyber-attacks, operation personnel faults and anomalies inside an industrial network. All prevention and detection technologies are managed via a single centralized management console.
Specialized security services for critical infrastructure
The Kaspersky Industrial CyberSecurity solution enables a broad range of protection to help infrastructure operators build an efficient security strategy. This means going beyond threat detection and prevention technologies by adding specialized security services to develop incident response and prediction capabilities.
An efficient approach to security always starts with industrial cybersecurity training, both for IT security professionals and general employees (awareness programs), aiming to target the personnel awareness gap and mitigate the risks of human error. Awareness training programs include baseline security in ICS, social attack in critical infrastructure environment and others. Expert services include cybersecurity assessment and penetration testing. These services allow customers to strengthen their own intelligence, manifest the most critical vulnerabilities, including zero-day threats, and predict cyber-threats relevant to the company’s specific industrial assets and technological processes. Incident response services delivered by our dedicated industrial cybersecurity team all around the globe will help to localize the intrusion, mitigate consequences, stop attackers from penetrating further into the infrastructure, prevent subsequent attacks on a compаny and develop an incident response plan for the future.
Meeting the strict industry requirements
The highly customizable settings of Kaspersky Industrial CyberSecurity mean it can be configured in strict accordance with the requirements of different industries, facilities and production lines, allowing the solution to be effectively integrated into an organization’s existing ICS network and technological processes without any significant modifications to the network or to the process. All of the company’s technologies are tested by and certified with leading ICS vendors.
When Kaspersky Lab is developing our specialized security software for industrial facilities, there are some unique requirements we had to meet:
- Observability mode. Security solutions are deployed extremely carefully in critical industrial environments. Solutions should be able to monitor activity and detect threats, but leave the decision to block an attack up to the operator. Industrial systems rely on customized software, so even the potential conflict between a security solution and, let’s say, operations of a railway system cannot be allowed. For a typical IT infrastructure this provides us with a good example of the careful deployment of a new feature – such as application control. Run it in the background, collect all of the stats, analyze and refine and only then – roll out full functionality.
- Security assessment. Critical infrastructure always works together with traditional IT, and the fact that different teams are usually responsible for security of those two entities is challenging. An independent look by security experts proficient in both industrial systems and general IT helps to identify potential weaknesses usually found at the meeting point between two systems. This is also true for any traditional IT infrastructure. In fact, the variety of endpoints, mobile devices, on-site servers and cloud services is no less complicated than a power plant.
- Exploit prevention. Technologies designed to identify attacks using previously unknown vulnerabilities is one level above traditional anti-malware systems. As we learned from Stuxnet, critical infrastructure may be targeted with the most advanced cyber weapons. Unlike traditional malware, targeted and advanced attacks require special tools. As we know, targeted attacks put businesses in danger even more than industrial facilities. So if you ask me, it was time to start protecting businesses from APTs yesterday.
These are the positive examples of critical infrastructure specifics that may be adopted by traditional businesses right away. But here are a few things that would be better if they stay within the manufacturing and energy sectors.
- Older hardware. It costs millions, it is reliable, and you can find fully operational machines still working under Windows 98. While there are reasons to use this hardware this in critical infrastructure, this is not an excuse to use outdated software and hardware in the office. When IT reaches its end of life, it’s worth replacing for the sake of security.
- Isolated operations. Letting a SCADA system directly connect to the Internet is the worst thing that can happen with an industrial system. For security it presents problems, especially in terms of the delivery of security updates. They can be solved, but isolating traditional infrastructure without changing the security approach leads to a lot of trouble.
The best takeaway from mission-critical experience is the need to have the right attitude. When you know that the wrong software update can cause an hour’s outage and losses of thousands of dollars per minute, you have to alter your approach. Traditional IT is usually more relaxed, although it is possible to lose anything from $66K (SMBs) to $1,4M (enterprises) due to downtime from a security incident. Given this, adopting a ‘critical’ attitude when thinking about IT security seems to be a wise choice.
More detailed information about Kaspersky Industrial CyberSecurity is available here.